LastPass, one of the leading password manager software, has experienced a series of data breaches that have users worried about their cybersecurity.
“Based on our investigation to date, we have learned that an unknown threat actor accessed a cloud-based storage environment leveraging information obtained from the incident we previously disclosed in August of 2022.”, LastPass management said in a blog post.
This set the stage for the second breach in November, which saw the hacker access LastPass’ third-party cloud storage. Using previously stolen keys and credentials in August, they were able to decrypt certain storage volumes, presenting a serious cybersecurity threat for users.
Although the number of customers affected is currently unknown, the leaked information includes basic customer account information and related metadata such as “company names, end-user names, billing addresses, email addresses, telephone numbers and the IP addresses from which customers were accessing the LastPass service.”
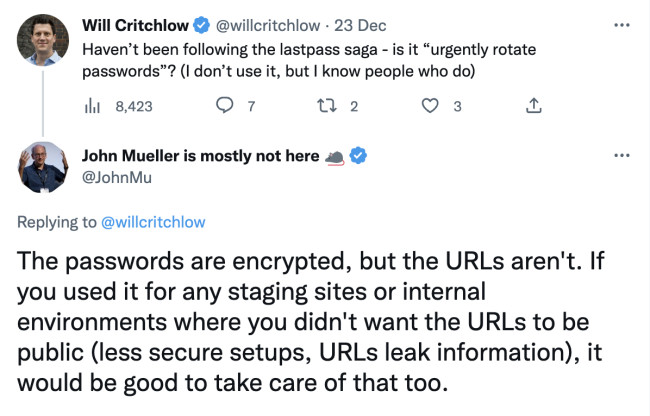
Meanwhile, Google’s Search Advocate, John Mueller, wrote in a tweet that while passwords are encrypted, the website URLs in the breach remained “unencrypted,” which means they can be published and accessed by bots. “It would be good to take care of that [URLs] too,” he added.
The latest update about the LastPass hacks gives the most serious cause for concern to date. The unknown hacker has also gained access to backup customer vault data, which includes both unencrypted data as well as sensitive and high-risk encrypted data like website usernames, passwords, secure notes and form-filled data.
Could this mean that LastPass’ master passwords are up for grabs? This would ring a serious alarm considering that more than 100,000 businesses and 33 million individuals use the software.
LastPass reminded customers that all encrypted files are “secured with 256-bit AES encryption,” making the possibility of decryption highly unlikely. The company detailed in a blog post that the malicious actors would have to use “brute force” to decrypt the stolen files and that “it would take millions of years to guess a master password using generally-available password-cracking technology.”
While that does bring some relief, it is still important to be mindful of phishing attacks following data breaches. Although LastPass insists that customers do not need to take any special measures to protect themselves at this time, the company stated that users that do not use the recommended default settings for their passwords should consider changing them to ensure safety.








-preview.jpg)
